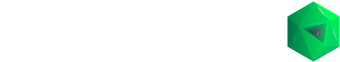
Initial Coin Offering Platform – Back-Office Features
Safe and Fast User Auth/Registration
We implemented a safe and user authentication and registration with real-time fields validation.
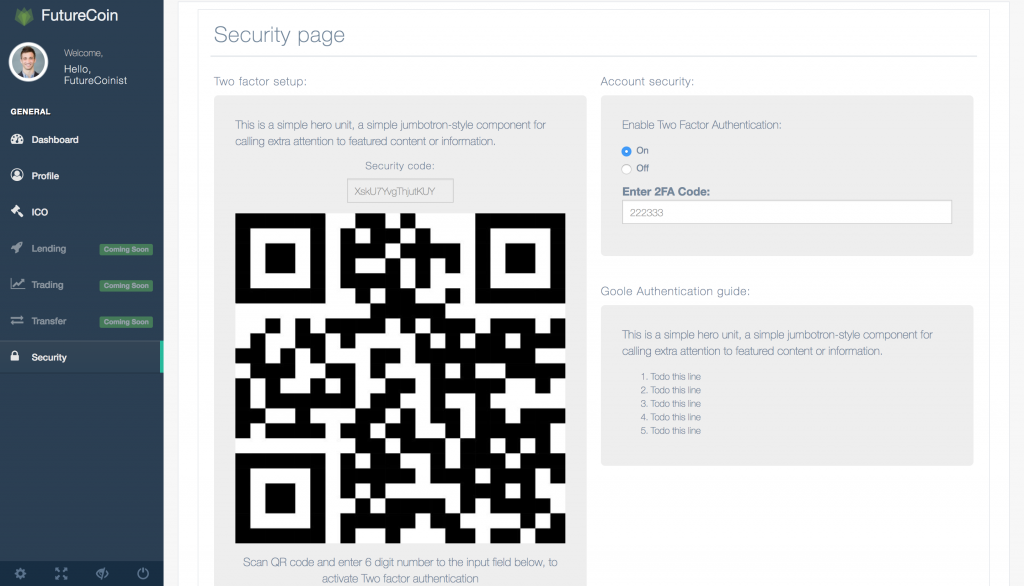
Two-Facto-Authorization
Also we added Two-Factor-Authorization to make it much harder to compromise user accounts and make fake transaction or stole users funds.
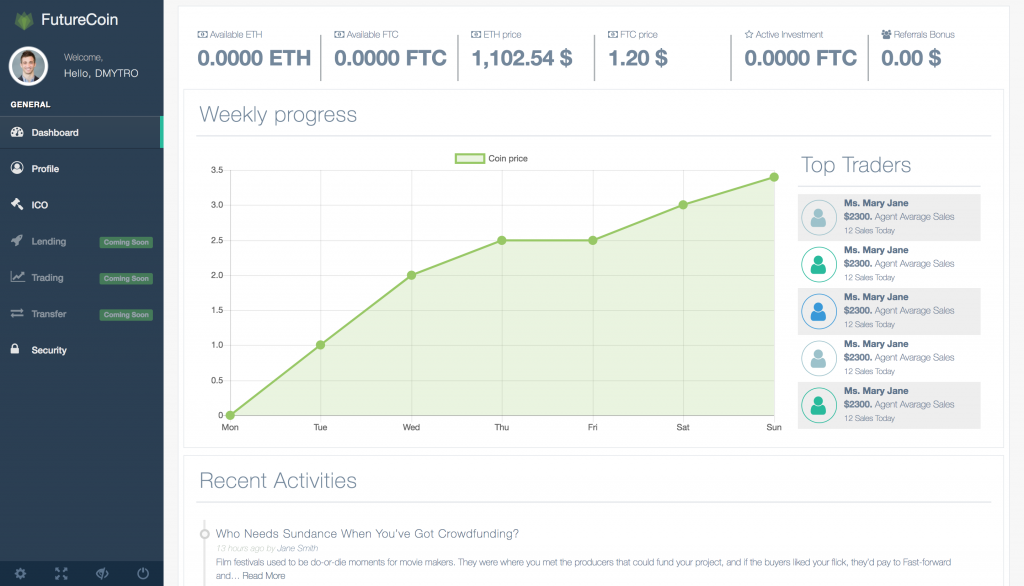
Initial Coin Offering Functionality
Initial Coin Offering page allows user to buy tokens easy and fast – all transactions will be conducted in the background by another part of platform.
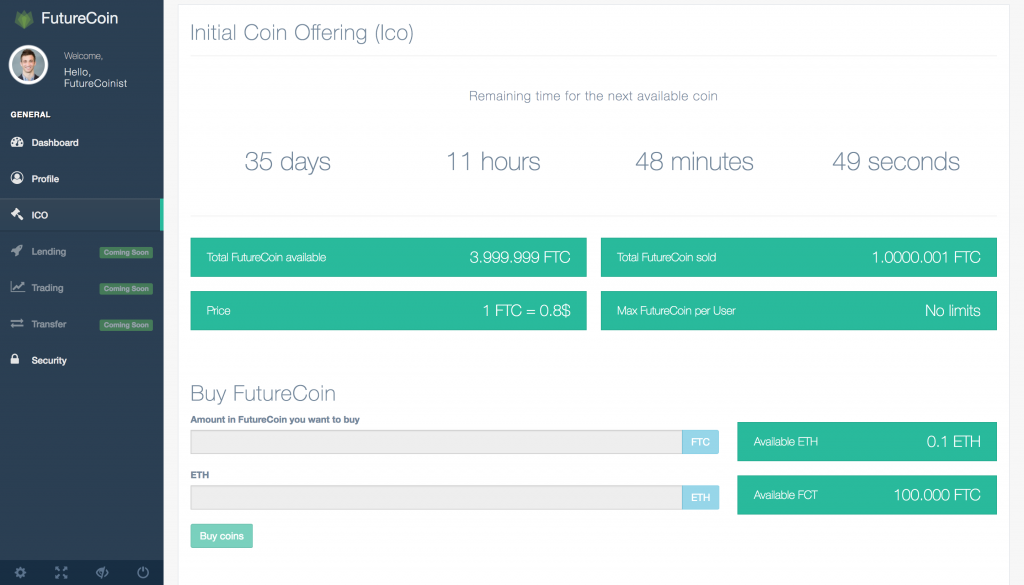
User Profile and Monitoring Tool
User profile allows you to see and modify your personal data, to get your Ethereum address and to track all activity of your account. Ethereum address is hosted in your personal wallet on our service.
Concurrency
All transaction will be processed in background by our third-party secure and fast service. So you can be calm about your funds.
More Features
There is also another additional functionality available… stay tuned to get more!